SITE, Privafy Announce JV for delivery of Extended Detection and Response solution in the kingdom.
At Privafy we took a hard look at the existing IPSEC and SSL/TLS landscape and said “we can do better”. With this in mind, we are shared the problems with today’s open and overly flexible VPN. In a format designed for clarity, we also proposed solutions to ensure the best possible data-in-motion protection for your site-to-site and client-to-site traffic.
Problem: Dissemination and deployment of private keys or PSKs to devices can open a myriad of compromise points exposing the entire network to decryption. This includes leakage of shared configuration information, CA compromise, one key to rule them all, etc.
Solution: With Privafy, private keys are unique in each direction on each peer, all keys are exchanged out of band via cloud, and are rotated every 24 hours. Privafy also maintains its own CA and device attestation certificates to remove the possibility of a third party CA compromise. With all this, compromise of a key is extremely unlikely and if it does occur exposure would be most likely one direction of one peer for a matter of hours.
Problem: Configuration errors can allow for less secure deployment. Keys are reused and not rotated due to human element. External Orchestration systems to negate this issue are expensive and cumbersome.
Solution: Privafy manages all aspects of key management and tunnel configuration. Human error is removed from the equation, and orchestration is built in, not external with its own configuration management issues.
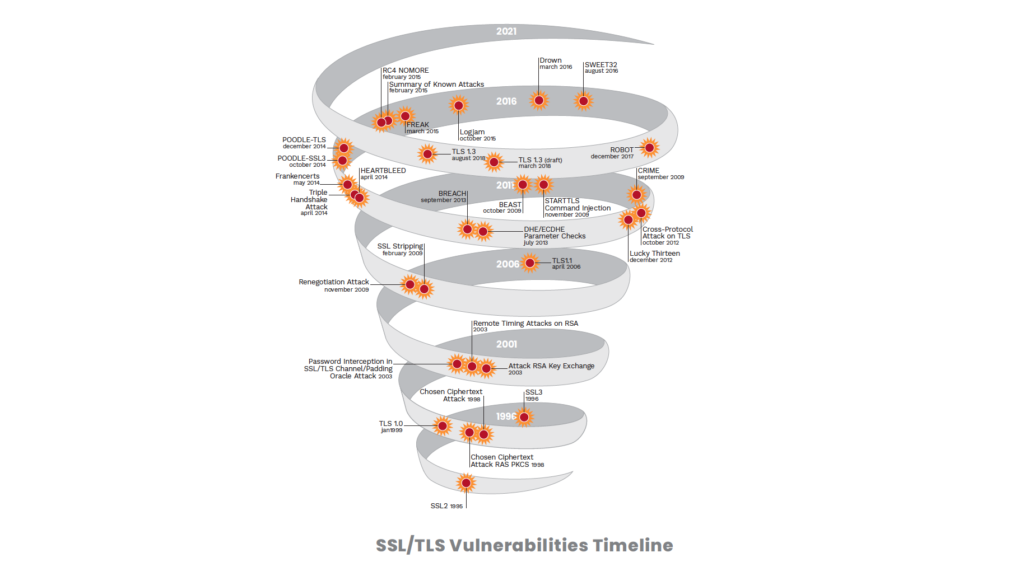
Problem: Old and deprecated encryption standards can be forcefully negotiated by bad actors to allow for easier decryption.
Solution: Privafy does not negotiate Cipher; only AES256-GCM is used.
Problem: NAT Traversal and IPSEC ACLs can be troublesome to manage and can offer new attack surfaces.
Solution: Privafy uses control channel to discover NAT pinhole and no static NAT or ACL configurations have to be managed.
Problem: Compliance standards such as PCI and HIPAA emphasize the need for key management, key rotation, and auditable ledger of key maintenance.
Solution: Privafy manages this process end-to-end and maintains an immutable ledger in blockchain for auditing and compliance purposes.
Problem: Endpoint VPN connections require static configurations that can be complex to convey, do not survive infrastructure changes, and can potentially leak sensitive information such as keys and passwords during initial setup.
Solution: Privafy AppEdge is dynamically configured at time of connection to use the most appropriate edge device as its access gateway to allow for the best traffic path and reroute/recovery from device failures. No configuration information beyond activation key is required for end users to bring their endpoint online. This means less complexity and more security through obscurity.
To learn more about how Privafy can help you avoid the pitfalls of TLS/SSL, check out our latest whitepaper, “Private Internets: The Future of Secure Connectivity.”